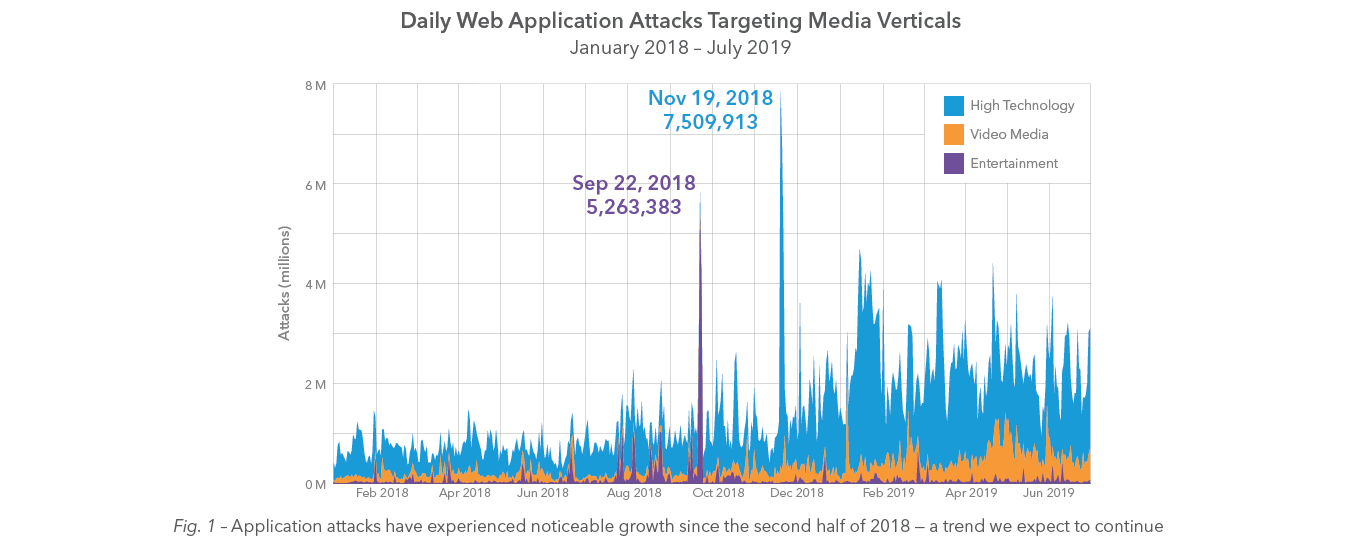
From January 2018 through June 2019, Akamai recorded more than 61 billion credential stuffing attempts and more than 4 billion web application attacks. In this special edition of the State of the Internet / Security Report, we’re focusing on data within the high tech, video media, and entertainment sectors — collectively named Media & Technology. These three industries accounted for nearly 35% of all credential stuffing attacks, and almost 17% of the web application attacks seen by Akamai during the 18-month reporting period. Our analysis indicates these three verticals are a stable and consistent attack source for two reasons: personal and corporate data. The targeted brands are household names, and criminals are looking to capitalize on that familiarity.
By attacking directly via web application attacks, criminals hope to expose customer records and financial data or leverage a vulnerable server to spread malicious code — also a common motive driving criminals to attack the retail sector. Credential stuffing abuses the brands targeted, as well as their customers, enabling the criminals to target personal information and corporate assets, such as media or digital products.
„One of the biggest fears that broadcasters have is “black to air” — the moment when all the viewer sees is an empty screen. From a security point of view, Internet-based attacks such as Distributed Denial of Service (DDoS) are risks that broadcasters now have to think about across the supply chain. These are risks that have been around for decades in industries such as financial services. The new world of live IP TV, where much of the world’s media is consumed, means that any attack on availability could result in subscriber retention issues, hit ad revenue, and reduce the chances of future successful bids for rights.“ (Jaspal Jandu, Group CISO, DAZN)
The full reports table of contents:
- Overview
- Guest Essay: Same Attacks, Different Risks, Global Impact
- Web Application Attacks
- Credential Stuffing
- Methodologies
- Credits
Download "Media Under Assault" - SOTI Volume 5, Special Edition Report
(PDF, English, 20 Seiten)
